Figure 1 from PIR-Tor: Scalable Anonymous Communication Using Private Information Retrieval | Semantic Scholar
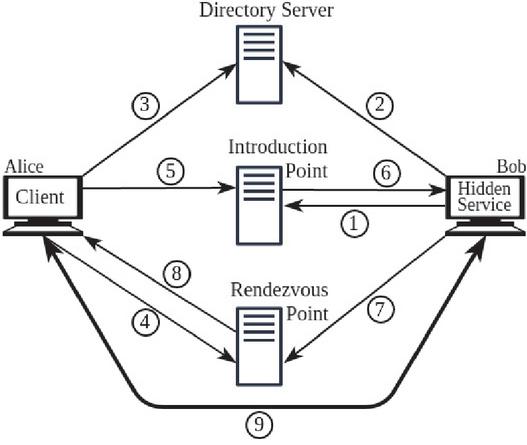
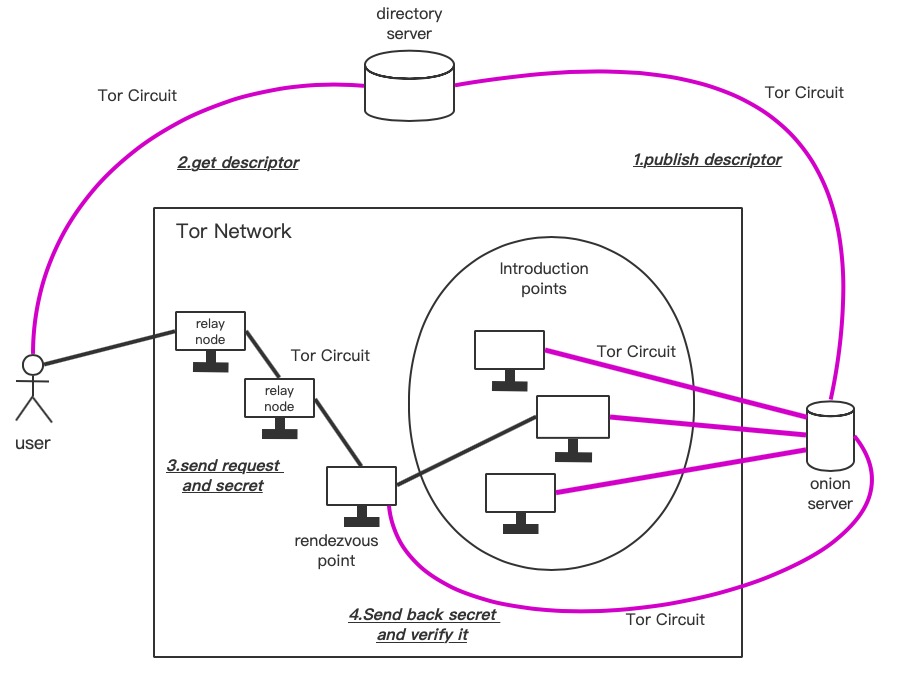
What is the difference between a directory server and a hidden service database? - Tor Stack Exchange
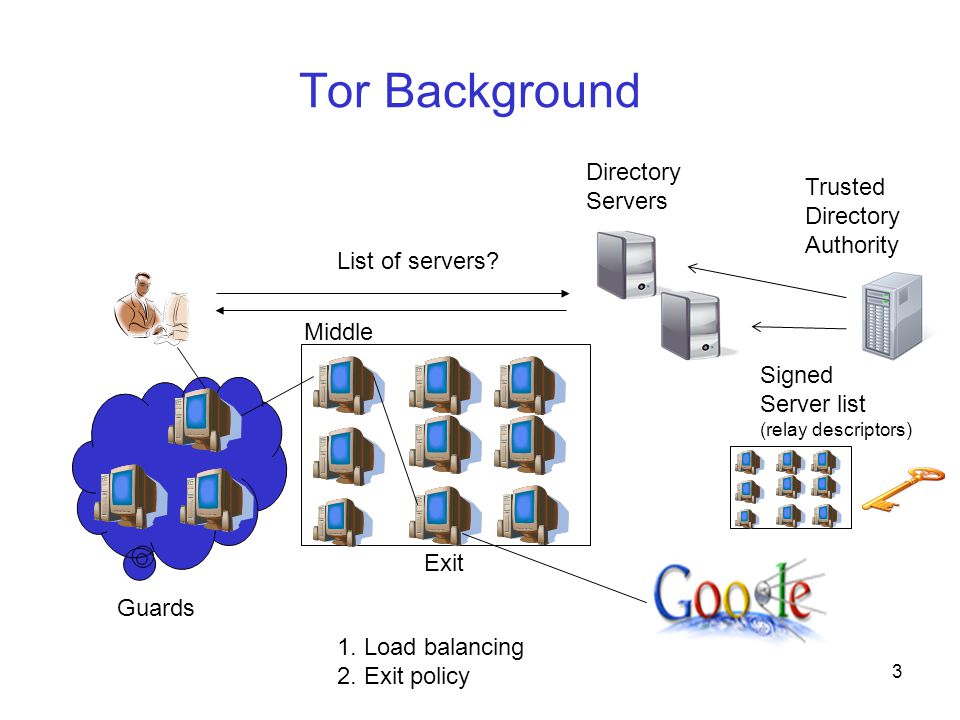
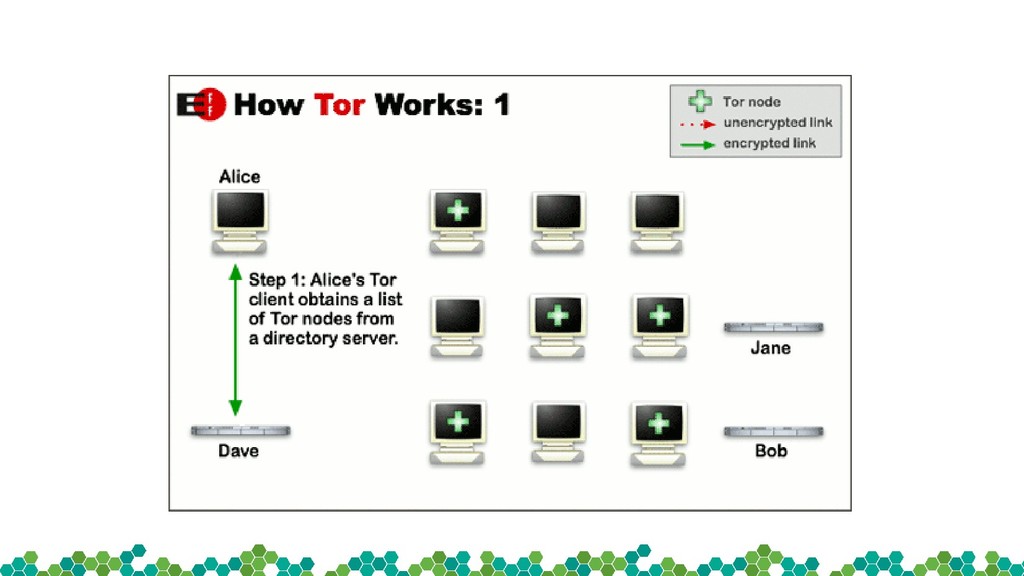
PIR-Tor: Scalable Anonymous Communication Using Private Information Retrieval Prateek Mittal University of Illinois Urbana-Champaign Joint work with: Femi. - ppt download


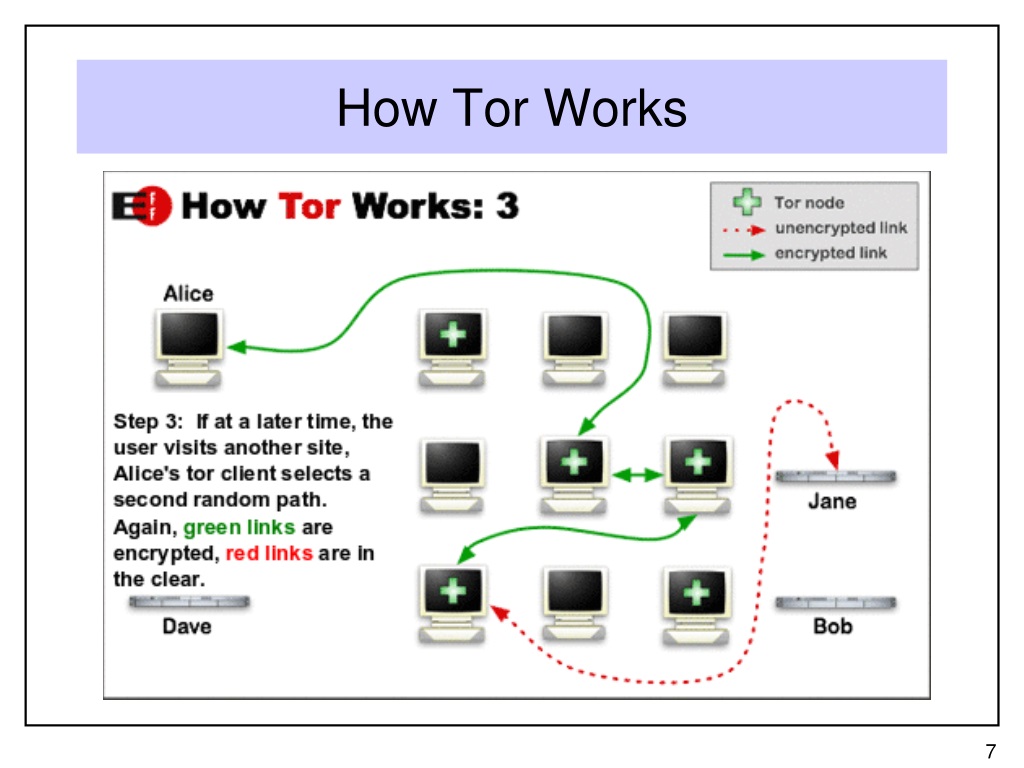




![Hacking the Tor network: Follow up [updated 2020] - Infosec Resources Hacking the Tor network: Follow up [updated 2020] - Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/010615_1141_HackingtheT1.png)